Blog
Unveiling the Dynamics of Cyber Threats: Insights from a Global Honeyfarm
Introduction
Honeypots have long served as indispensable tools in the realm of cybersecurity, offering a means to detect, monitor, and comprehend unauthorized attempts to breach information systems. Over the years, they have been used to characterize malware, such as the notorious Mirai, as well as to determine points of interest targeted by intruders.
In this article, we delve into a groundbreaking study that provides valuable insights and benefits derived from a large operational honeyfarm—a network of honeypots strategically distributed worldwide, with centralized data collection.
The Global Reach
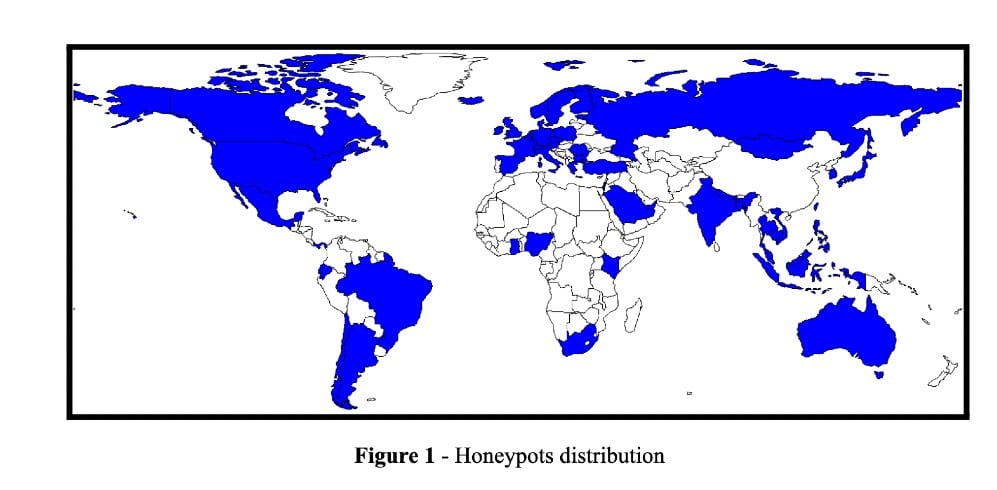
Our research spans over a 15-month period, analyzing a staggering volume of 400 million sessions collected from 221 honeypots deployed across 55 countries (see Figure 1). This global perspective enables us to unravel stark differences in the activities observed by these honeypots. Some are inundated with millions of contact attempts, while others quietly observe only a few thousand sessions.
Scanners, Scouters, and Intruders
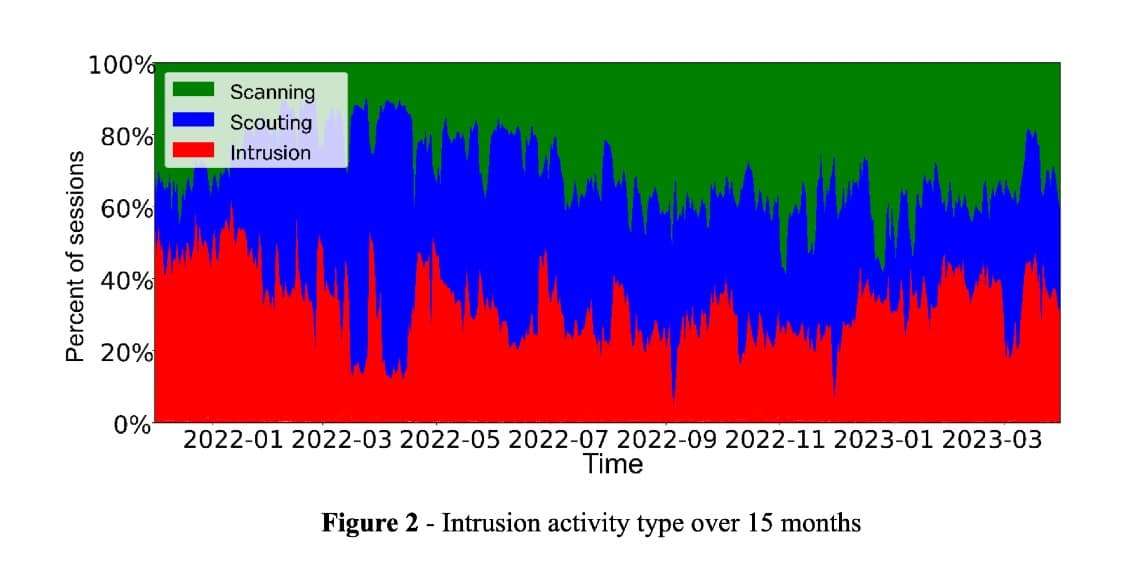
While all the contact sessions recorded by the honeypots are unwanted and should not be trusted, we should make a clear difference between the three interaction types found— Scanners, Scouters, and Intruders.
As their name suggests:
Scanners are entities that did not try to login or execute any commands in the recorded sessions.
Scouters are entities that tried to login at least once in the recorded sessions, but did not succeed.
Intruders are entities that successfully logged-in and gained access to execute commands in the recorded sessions.
Our analysis starts with the inception of a new honeyfarm, offering a unique perspective on its development over 15 months.
As we delve into the data, we observe that the levels of scanning and scouting closely mirror intrusion activities during the initial stages. However, a notable shift occurs over time, with scanning and scouting surpassing intrusion activity, showcasing the evolving focus of attackers (see Figure 2).
The second most important observation of this investigation is that we notice a significant amount of entities (client IPs that initiated the connection to the honeypot) having multiple roles, e.g. being both Scanners and Scouters or Scanners and Intruders. This nuanced understanding of honeyfarm dynamics is essential for refining strategies and fortifying defenses.
Intruder Behavior and File Diversity
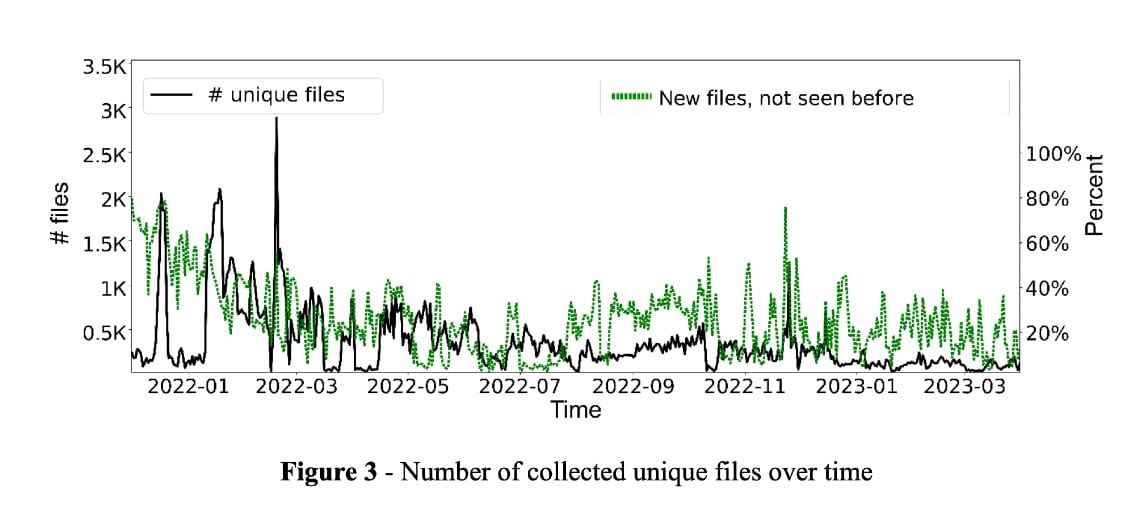
Analysis of intruder behavior reveals that they generate a multitude of different files.
Interestingly, no honeypot observed more than 5% of all unique files, emphasizing the importance of scale and diversity in honeyfarm deployment to capture the tail of more intriguing intrusions.
While many attacks based on hashes are visible for an extended period, their variations and the emergence of new attacks on a daily basis challenge easy detection (see Figure 3).
Some attacks consistently target the same subset of honeypots with a few client IPs, presenting a relatively straightforward takedown opportunity. In contrast, attacks utilizing many client IPs, likely from major botnets, pose a more formidable challenge but may offer valuable insights for tracking down botnets.
Honeyfarms and Security Realities
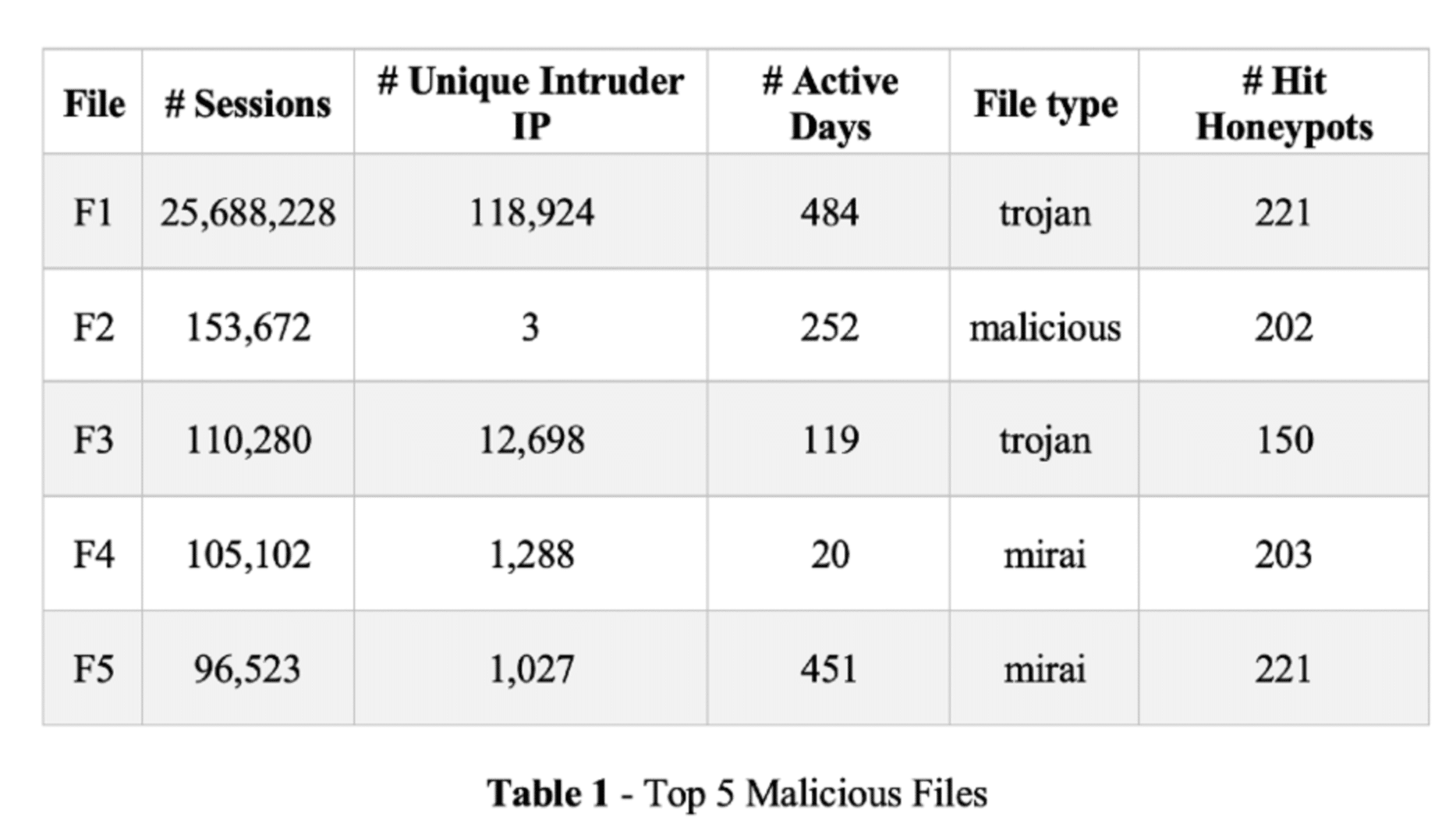
Our analysis of honeyfarm data unveils a striking reality— the majority of honeypots within the network observe high-profile attack campaigns.
Lasting for weeks to months, some campaigns are well-orchestrated, involving numerous IPs. However, we also identify prolonged campaigns spanning over half a year, originating from only a handful of IPs (see Table 1).
What is concerning is the apparent lack of action to block these IPs participating in extended campaigns. Our findings indicate that network and cloud providers might be inadequately informed or lack the necessary filters to prevent client IPs from engaging in scouting, intrusion, or interaction with potentially vulnerable hosts.
A Call for Collaboration
We advocate for collaborative efforts within the research and security community to address critical gaps in network defenses.
While honeyfarms prove to be highly effective in detecting attack campaigns, they are only one link in the chain of defenses. Federated honeyfarms, with shared data and intelligence, have the potential to offer a more comprehensive defense against cyber threats.
By bridging the gap between individual honeyfarms and pooling collective insights, we can work towards a more resilient cybersecurity infrastructure.
Implications and Conclusion
The discovery of multi-role client IPs engaging in various security-threatening tasks underscores the evolving nature of cyber threats.
The prolonged study of our honeyfarm, encompassing its entire lifespan, provides valuable insights into the resilience of attackers and the challenges posed by distributed honeypots.
As we continue our exploration, it becomes evident that the collaborative efforts with operational honeyfarms and the prolonged collection of data are imperative for staying ahead in the ongoing battle against cyber threats.
Our findings do not only contribute to academic knowledge but also offer practical implications for fortifying information systems against the relentless and adaptive nature of modern cyber adversaries.
If you want to learn more about this work, please read our paper presented at AMC IMC 2023 here.
Cristian Munteanu is the main author of the first research paper with Max-Planck-Institut für Informatik using AIDE. You can connect with him on LinkedIn.


