DANE
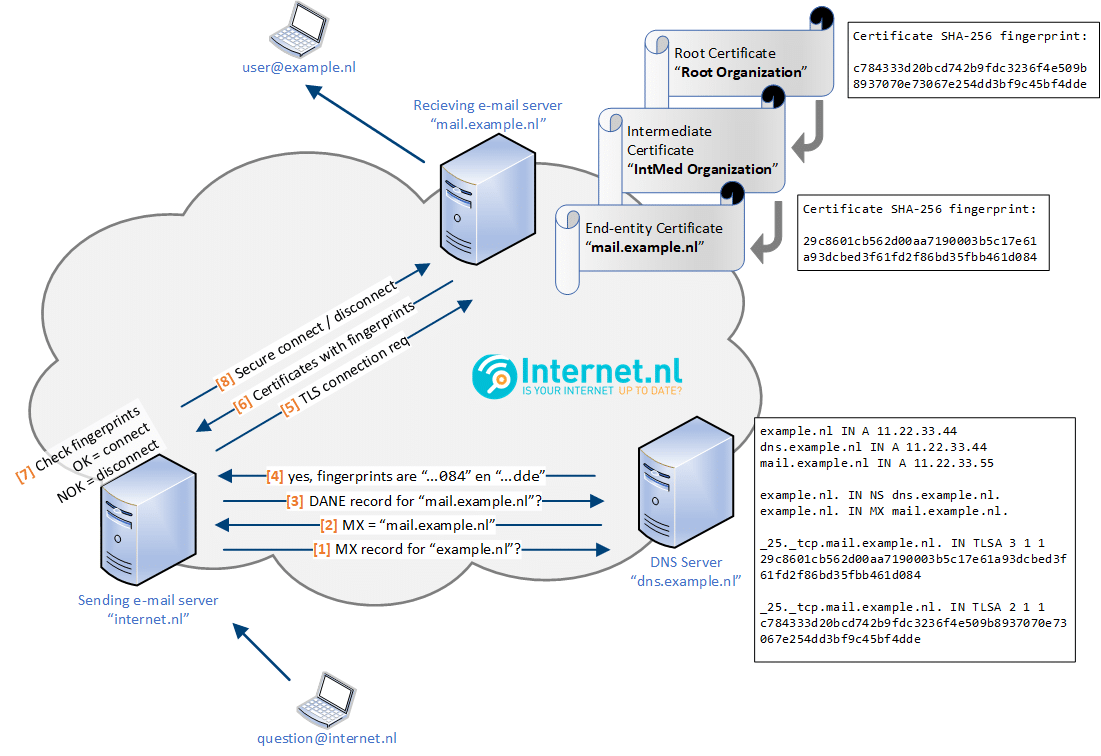
DNS-based Authentication of Named Entities (DANE) for SMTP addresses allows for a more secure method of mail transport. DANE allows SMTP servers to establish encrypted TLS connections without the disadvantages of STARTTLS. DANE is used to ensure reliable encryption for email transport. For this to work as intended, DANE uses the secure version of the Domain Name System (DNSSEC) for retrieving information that is published by a domain name’s owner or administrator. As a result, this information enables SMTP servers to determine up front whether or not another SMTP server supports an encrypted connection while also providing the means of validating the authenticity of the other mail server’s certificate. Confidentiality of email is available to the masses.