Blog
Indian Threat Landscape and How Organizations Can Secure Themselves
By Bhavin Bhansali, Founder & CEO, ProgIST Solutions
The Problem Statement
Considering the drastic growth in e-commerce and Internet activity, cybersecurity is a major issue in developing countries like India. Securing businesses is a challenge faced by major Indian organizations, irrespective of their operations being small, medium, or of a large scale. With the COVID-19 pandemic on the roll, the sudden mandate to work remotely makes it even more challenging.
New technology-led business models and increasing digitization have become a medium for potential cyber threats to land on a broader surface, requiring enhanced cyber risk management. The adoption of emerging technologies such as chatbots, artificial intelligence, blockchain, and the cloud results in organizations spending equal amounts or even more on cybersecurity.
With the systems getting more interconnected, a significant increase is seen in the number of breaches and sophisticated cyberattacks, driven by various motives. This is evident from the rise in cyberattacks reported by the Indian Computer Emergency Response Team (CERT-In) — from 53,081 in 2017 to 208,456 in 2018, an increase of about 392%.
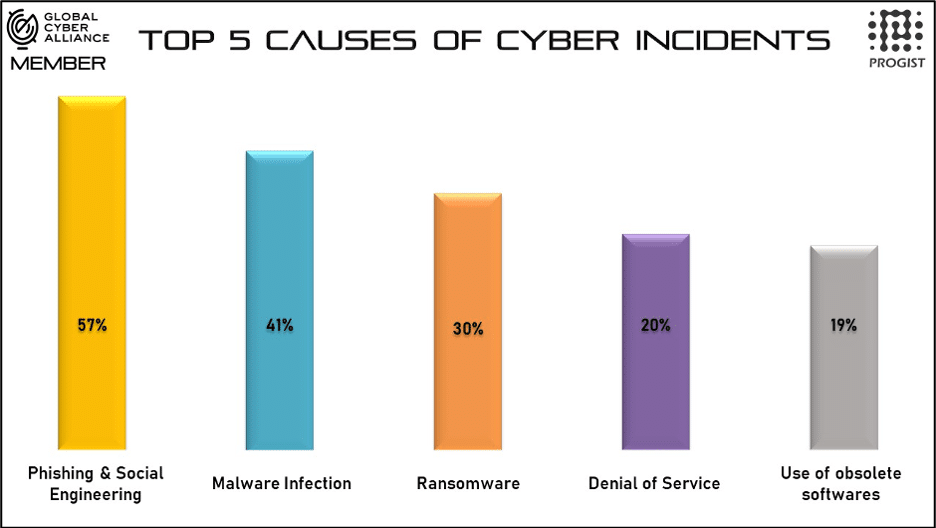
Over the years, cyberattacks have evolved to become sophisticated in nature, and types of attacks such as Advanced Persistent Threat (APT), zero-day, malware, ransomware, and multi-vector attacks have become common, targeting the core infrastructure of organizations.
Keeping in perspective the current cybersecurity landscape, major businesses in India are building stronger defense mechanisms to combat ever-evolving cyberattacks and threats — not only from the regulatory requirement perspective, but also as a proactive self-initiative to boost stakeholder and customer trust.
At a constant pace, cybersecurity must now not only address deliberate attacks, such as those from disgruntled employees and industrial espionage, but also cover inadvertent compromises of the information infrastructure due to user errors, equipment failures, and natural disasters. Regulatory requirements, risk of reputation loss in case of data breaches, and loss of competitive advantage owing to data loss are some of the key factors driving Indian organizations’ investments in data security and privacy.
As a result, the expectation from cybersecurity solution providers is for organizations to broaden their scope with regards to consultancy, conducting maturity assessments, providing tools and services that can bolster an organization’s defense against cyberattacks and threats, cultivating all employees with cybersecurity awareness, and carrying out forensic assessments in case of an incident.
In summary, organizations are burdened to secure not only their employees but also to protect their communications and integrations with third-party service providers with whom organizations outsource certain activities, partners, distributors, suppliers, and the entire ecosystem revolving around it.
What Can Organizations Do?
Improving your company’s cybersecurity doesn’t have to be overwhelming or costly. To enable business owners to significantly reduce the cyber risks faced on a day-to-day basis, the Global Cyber Alliance (GCA) has built a toolkit to address the Center for Internet Security (CIS) Controls. The Cybersecurity Toolkit for Small Business can be used by organizations to assess their security posture, implement appropriate open-source tools, find practical tips, and use free resources and guides to improve their company’s cybersecurity readiness and response.
The toolkit focuses on simple, yet effective steps to be followed by organizations to achieve a mature cybersecurity structure.
- It starts with the basic principle of knowing what you have — the first step to better security. Identify all organization-owned devices (including desktops, laptops, smartphones, printers, etc.) and applications (email client, operational software, web browsers, websites, etc.) so appropriate measures can be taken to secure them. Maintaining this inventory will serve as a guide and checklist as organizations make their way through the rest of the toolboxes.
- With each hardware and software component identified, the next step is to boost digital immunity against threats such as viruses, spyware, and others is to keep your systems updated. Although most devices and applications can be configured to automatically update, it is recommended to use a holistic approach towards keeping the patches up to date.
- The next step is to think beyond simple password-based authentication — in simple terms, to lock your virtual doors and windows. Your accounts and data (such as emails, personnel records, or client databases) are valuable assets — to you as well as to cyber criminals. Keep your accounts safer by moving beyond simple passwords and use strong passwords with multi-factor authentication (MFA) — an additional layer of protection for your passwords. Be sure to set up unique passwords on all your accounts and define a dedicated policy for password management.
- Preventing phishing and viruses entering your organization’s ecosystem is the later stage bolstered by the toolkit. Every year many businesses fall victim to costly malware and phishing attacks, resulting in difficulty to survive. These attacks can infect organizations in revenue loss, expensive recovery costs, data loss, damage to reputation, and more. The solution? Setting up Domain Name System (DNS) security by using Quad9 to help prevent organizations from navigating to infected websites. Quad9 is an effective and easy way to add an additional layer of security to your infrastructure for free — helping organizations route their DNS queries through a secure network of servers around the globe. This step also includes procuring anti-virus software to help prevent viruses and other malicious software from getting into your systems and ad blockers to help prevent online advertisements, which can carry viruses.
- Defending against ransomware and malware — the procurement of solutions that protect against ransomware infection — can be a costly and yet ineffective affair. The simple solution to defend against ransomwares is to maintain up-to-date backups for recovery from these attacks. Additionally, organizations can ensure that the backups don’t stay connected to the original source of the data-storing computers/servers.
- Protecting the reputation and brand of your business is critical to an organization’s success. Organizations can help do this by implementing tools that ensure their brand’s name and email addresses don’t get used by others pretending to be them. An email standard known as DMARC is an effective way to stop spammers and phishers from using company domains to carry out dangerous cyberattacks. It’s a proficient way to verify that the sender of an email has permission to use your email domain and send email. Using known DMARC analytics tools, organizations can address issues pertaining to business email compromise (BEC) — a targeted email attack — which is a growing threat to companies. A side benefit to using DMARC protection is that it may lead to better delivery of email to your customers’ inboxes instead of to their spam folder.
The author, Bhavin Bhansali, is the Founder & CEO of ProgIST Solutions, a GCA partner. You can connect with him on LinkedIn.
Editor’s Note: The views expressed by the author are not necessarily those of the Global Cyber Alliance.
cybercyber securitycybersecurityGCA Cybersecurity Toolkit for Small BusinessGCA ToolkitphishingransomwareSmall business


