Blog
Tracing Volt Typhoon: Insights from GCA’s AIDE Honey Farm
As you may have seen in the news recently, the Volt Typhoon campaign is a cyber espionage group believed to originate from China. “A December 2023 court-authorized operation has disrupted a botnet of hundreds of U.S.-based small office/home office (SOHO) routers hijacked by People’s Republic of China (PRC) state-sponsored hackers,” said the US Department of Justice. Known for strategic attacks on global critical infrastructure sectors, the group uses advanced techniques to exploit vulnerabilities in network devices, especially those manufactured by Cisco and NetGear. Their focus lies in targeting SOHO routers and maintaining persistent access to target networks through known security weaknesses and default configurations. You can read more in this TechRepublic article, “Botnet Attack Targeted Routers: A Wake-Up Call for Securing Remote Employees’ Hardware.”
Despite clearing malware from outdated routers, the Volt Typhoon campaign has resurfaced, targeting crucial U.S. infrastructure sectors, including communications and energy, highlighting the ongoing cybersecurity challenge. The Volt Typhoon campaign serves as a vivid wake-up call to the hidden cyber risks that surround us.
When we learned about Volt Typhoon, we wondered if we could see the effects of those attacks on our Automated IoT Defence Ecosystem (AIDE) platform. AIDE collects Internet of Things (IoT) attack data through a distributed network of honeypots, with over 200 sensors deployed across 55 countries. This platform serves as a tool in cybersecurity, designed to detect and analyze unauthorized access attempts, profile malware, and pinpoint the whereabouts of intruders. It turns out we can see traces of the Volt Typhoon activity within AIDE, and here we’ll dive into some of the data and share our insights.
AIDE’s Data Insights
- IP Address Matches:
We found that 5.1% of IP addresses from the Volt Typhoon Indicator of Compromise (IoC) list, as published by Microsoft and SecurityScorecard, have actively interacted with sensors in the AIDE dataset. For more detailed information, you can refer to the Microsoft blog “Volt Typhoon Targets US Critical Infrastructure with Living Off the Land Techniques” and the SecurityScorecard report “SecurityScorecard Threat Research: Volt Typhoon Compromises 30% of Cisco RV320/325 Devices in 37 Days.‘”
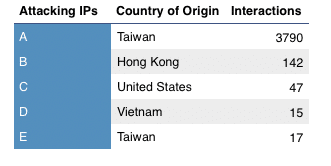
Figure 1: Volt Typhoon Activity Snapshot: Anonymized IP Address, Country of Origin, and Interaction Count.
Figure 1 displays the anonymized IP addresses (privacy reasons), their country of origin, and number of hits (interactions).
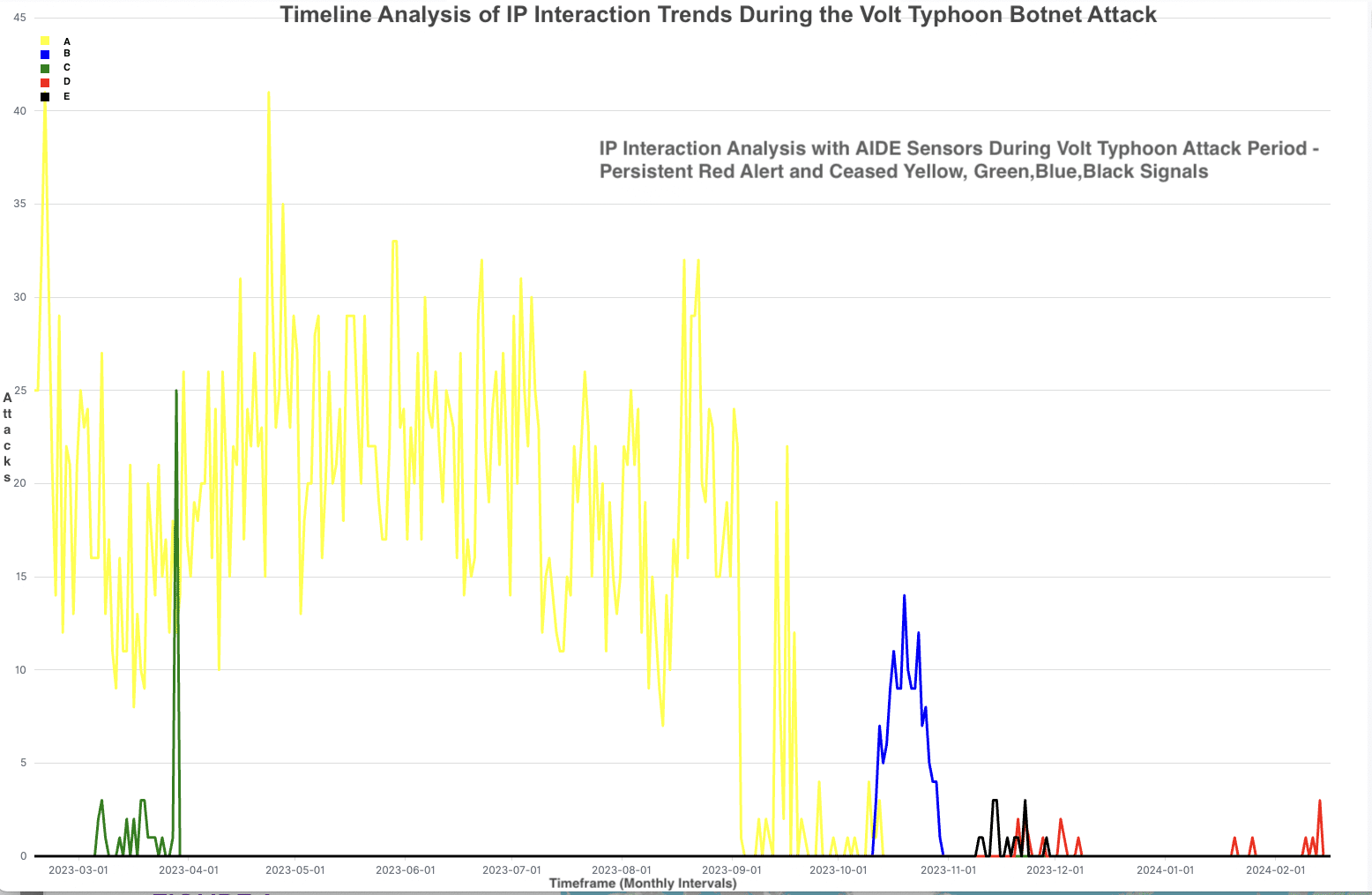
Figure 2: Timeline Analysis of IP Interaction Trends During the Volt Typhoon Botnet Attack
Figure 2 illustrates the trend of intrusions detected in the AIDE dataset. It highlights ongoing activity from the red signal (D), indicating recent attacks. In contrast, other colors, which represent other four IP sources, have ceased. These four ceased signals associated with IP addresses that have been blacklisted by several IP reputation checking services. Additionally, the red signal, which was last detected on March 7, 2024, according to Spamhaus, indicates that the associated machine has been infected with malware such as Hajime, Wopbot, or other Mirai family variants. These findings align with the observations mentioned in a TechRepublic article, where it was reported that Department of Justice investigators have removed malware from compromised routers.
- Geographical Distribution:
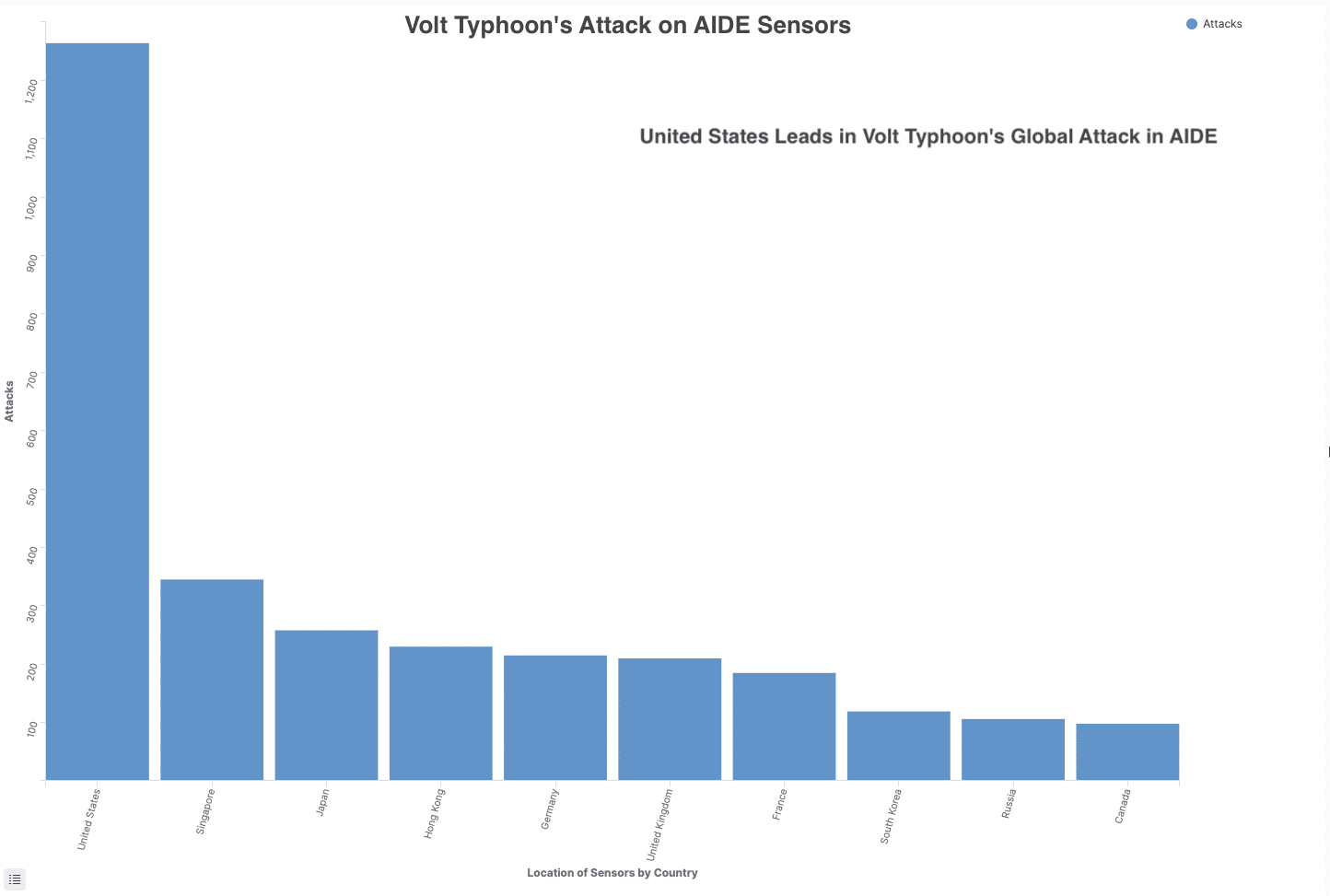
Figure 3: Volt Typhoon’s Attack on AIDE Sensors: United States Leads
The majority of these IP addresses targeted U.S.-based sensors, as illustrated in Figure 3, aligning with reports from the US Department of Justice.
- Executable File Surge:
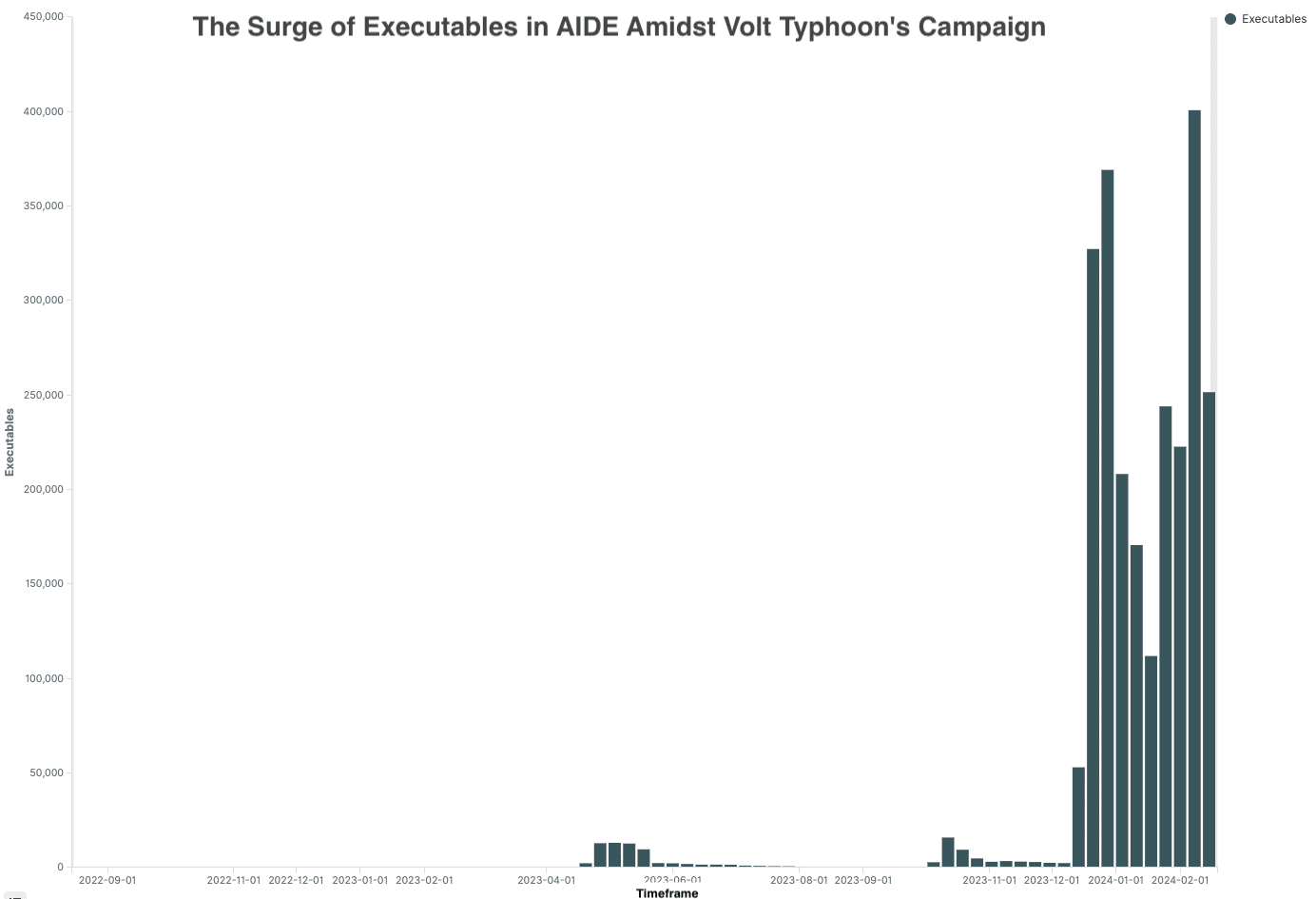
Figure 4: The Surge of Executables in AIDE Amidst Volt Typhoon’s Campaign
From December 2023 to January 2024, there was a notable increase in the use of suspicious executable files, coinciding with the reported time period for Volt Typhoon. Botnet attacks are frequently indicated by an increase in executables (instructions sent to a computer) on honeypots. These behaviors imply attempts to break into systems, gather information, or prepare for more significant attacks. Figure 4 illustrates the traffic trend associated with executable payload-commands.
- Credential Usage Patterns:
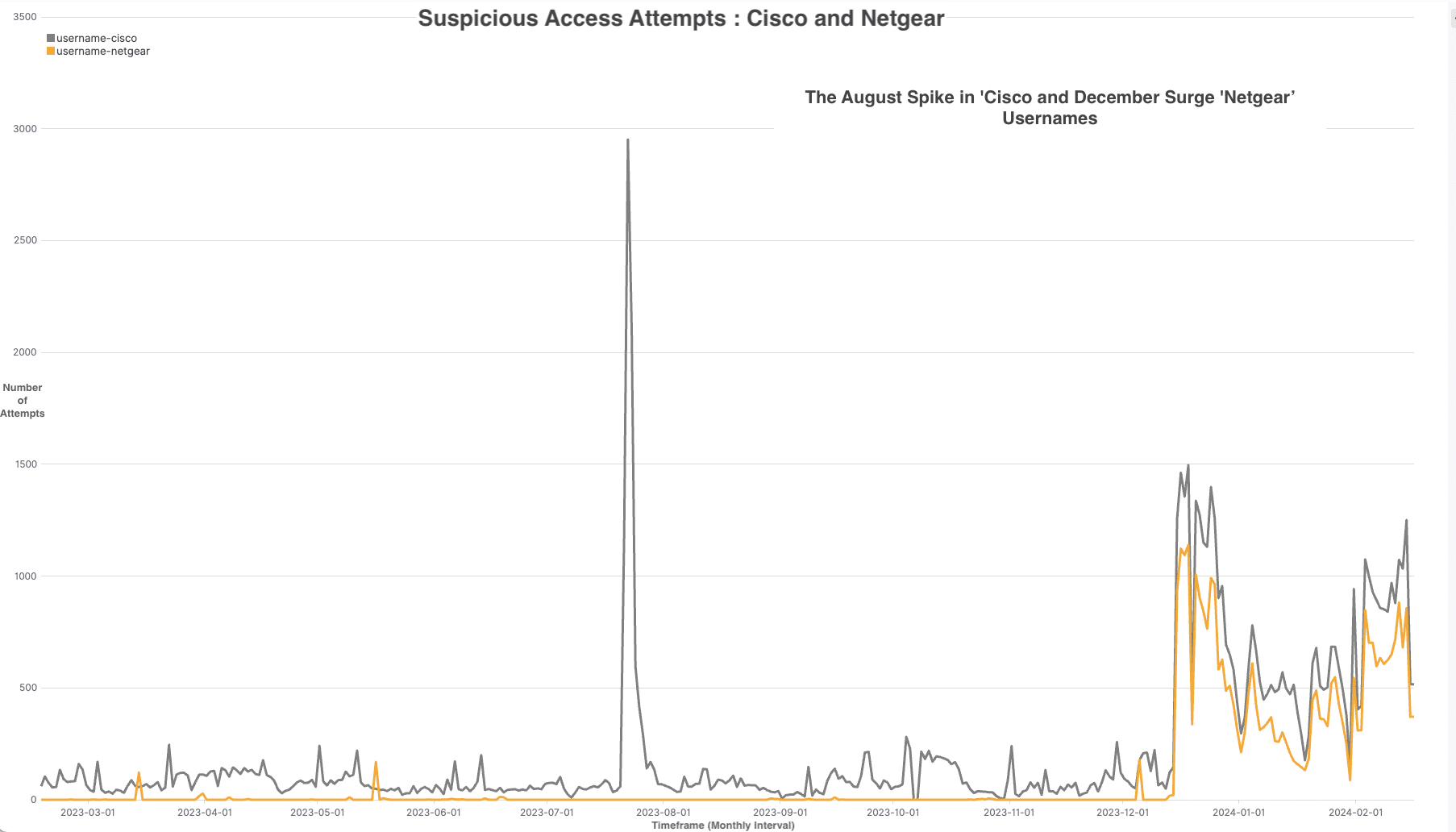
Figure 5: Suspicious Access Attempts: Cisco and Netgear
There was a significant surge in the use of ‘netgear’ and ‘cisco’ usernames within credentials, suggesting targeted attempts to exploit default configurations commonly associated with the devices such as routers. In other words, these home routers were never renamed or given unique passwords when put into use. Figure 5 highlights credential usage surge – the traffic spike, which was mostly caused by the username “cisco,” peaked in August 2023 and then declined. It then reappeared later in December 2023, but this time it was accompanied by the username “netgear.”
The Broad Nature of Attacks
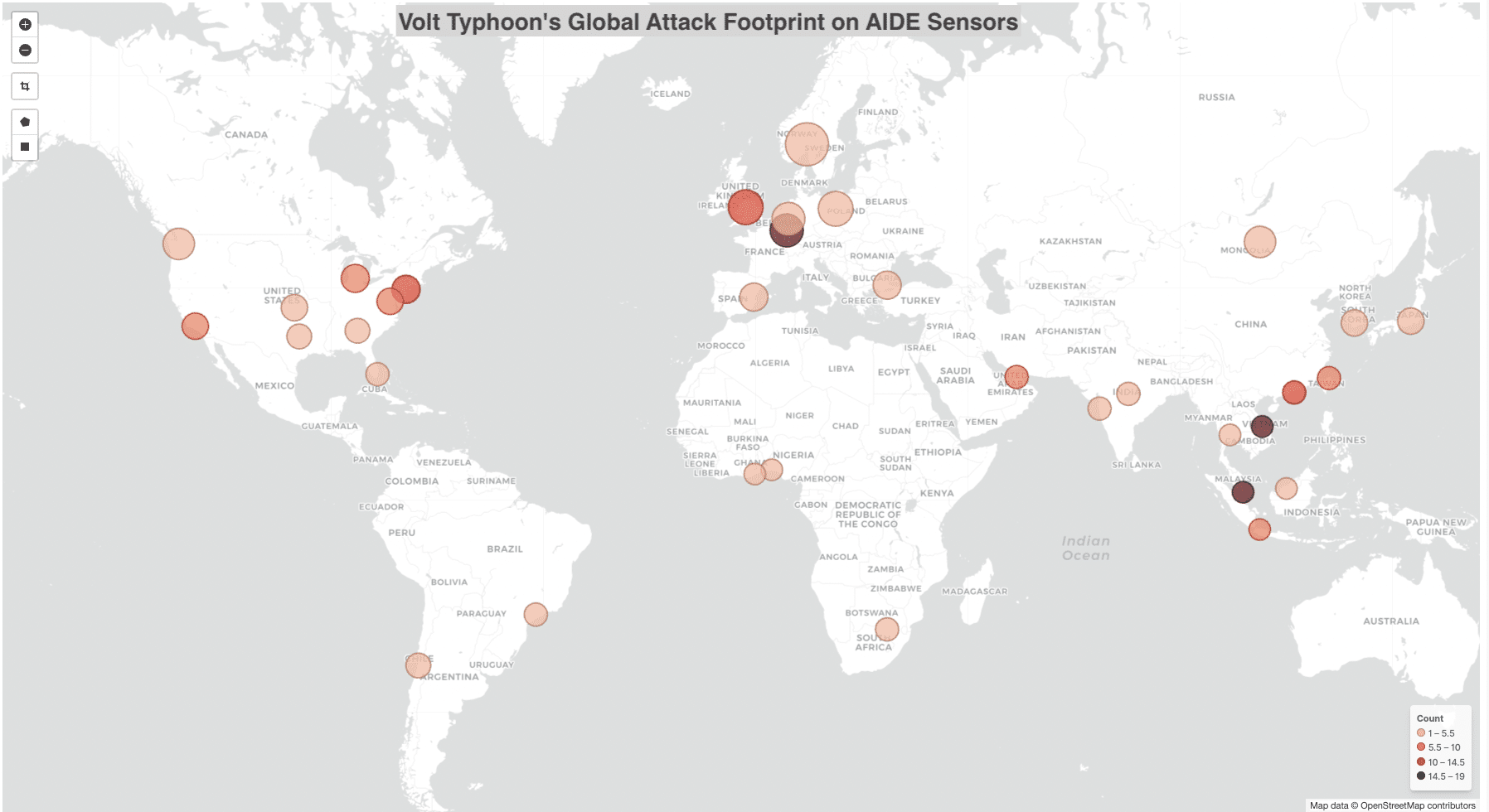
Figure 6: The geographical distribution of suspicious activities from attacking IP addresses on the AIDE sensors.
The traffic from the reported IP addresses associated with IoCs of infrastructure also reveals a broader attack footprint that includes sensors in multiple countries. This suggests a widespread campaign by Volt Typhoon, as seen in the AIDE dataset. Figure 6 illustrates the geographical distribution of suspicious activities from attacking IP addresses on the AIDE sensors.
Conclusion
The data collected by AIDE’s strategically placed sensors worldwide offers a comprehensive view into the vast and diverse landscape of threats against IoT devices like home routers. Some of the data in AIDE tells a compelling story: attacks are not limited to one location; they spread globally through networks. Our analysis delves into the unwanted traffic, revealing patterns and signatures that indicate not only how severe the problem is, but also where and how it is evolving. By sharing these insights and data feeds, we enable the ecosystem to mitigate attacks and foster a collaborative effort that enhances overall effectiveness on a wide scale.
The vast majority of routers that comprised the botnet taken down by the US Department of Justice were Cisco and NetGear routers that were vulnerable because they had reached “end of life” status; that is, they were no longer supported through their manufacturer’s security patches or other software updates. Read more on ‘Efficient Software Patching’ in the IoT Policy and Attack Report.
If you are interested in learning more about the AIDE project and would like to be part of its research community, either on IoT security or on unwanted traffic issues, contact us.
References
- CISA (Cybersecurity & Infrastructure Security Agency). “Cybersecurity Advisories: AA23-144A.” CISA, May 24, 2023. https://www.cisa.gov/news-events/cybersecurity-advisories/aa23-144a.
- Cisco Systems. “Access an SMB Switch CLI Using SSH or Telnet.” Cisco Systems, July 15, 2020. https://www.cisco.com/c/en/us/support/docs/smb/switches/Cisco-Business-Switching/kmgmt-2243-access-an-smb-switch-cli-using-ssh-or-telnet.html.
- Crouse, Megan. “Volt, Typhoon botnet attack: What security experts know so far.” TechRepublic, 9 February 2024. https://www.techrepublic.com/article/volt-typhoon-botnet-attack/.
- Microsoft. “Volt Typhoon Targets US Critical Infrastructure with Living Off the Land Techniques.” Microsoft Security, May 24, 2023. https://www.microsoft.com/en-us/security/blog/2023/05/24/volt-typhoon-targets-us-critical-infrastructure-with-living-off-the-land-techniques/.
- SecurityScorecard. “SecurityScorecard Threat Research: Volt Typhoon Compromises 30% of Cisco RV320/325 Devices in 37 Days.” SecurityScorecard, 2024. https://www.securityweek.com/wp-content/uploads/2024/01/Volt-Typhoon.pdf.


